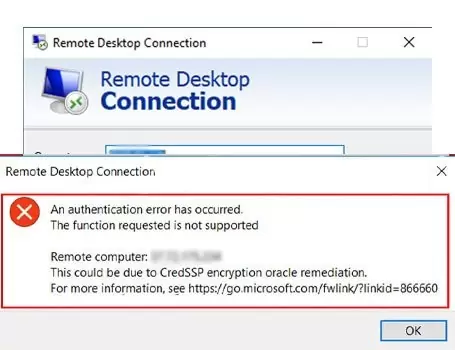
This error occurs if you are trying to establish an insecure RDP connection, and the insecure RDP connection is blocked by an Encryption Oracle Remediation policy setting on the server or client. This setting defines how to build an RDP session by using CredSSP, and whether an insecure RDP is allowed. To resolve the Remote Desktop Protocol (RDP) authentication error related to the CredSSP encryption oracle remediation on Windows OS, you can follow these steps:
How To Fix Remote Desktop CredSSP Encryption Oracle Remediation Error
Ensure your Client and Server Windows OS is up to date.
Update your Windows OS: Ensure that both the local and remote computers have the latest Windows updates installed. Microsoft often releases security patches and updates to address known issues, including CredSSP-related vulnerabilities. To resolve the issue, install CredSSP updates for both client and server so that RDP can be established in a secure manner. For more information, see CVE-2018-0886 | CredSSP Remote Code Execution Vulnerability.
Registry modification (for client-side):
- Press Win + R on your keyboard to open the Run dialog box.
- Type regedit and press Enter to open the Registry Editor.
- Navigate to the following registry key:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\CredSSP\Parameters
- If the Parameters key does not exist, you may need to create it.
- Inside the Parameters key, create a new DWORD value named AllowEncryptionOracle.
- Set the value of AllowEncryptionOracle to 2 (hexadecimal).
Group Policy modification (for server-side):
- Press Win + R on your keyboard to open the Run dialog box.
- Type gpedit.msc and press Enter to open the Local Group Policy Editor.
- Navigate to the following policy:
Computer Configuration -> Administrative Templates -> System -> Credentials Delegation -> Encryption Oracle Remediation
- Double-click on “Encryption Oracle Remediation” to open the policy settings.
- Select the “Enabled” option.
- Under “Options,” choose “Vulnerable” or “Mitigated” based on your security requirements. Selecting “Vulnerable” allows insecure clients to connect, while “Mitigated” only allows secure connections.
- Click OK to save the changes.
Restart your computer: After making the necessary changes in the Registry Editor or Group Policy Editor, restart your computer to apply the modifications.
These fixes above should resolve the error if you see the Remote Desktop Protocol (RDP) authentication error related to the CredSSP encryption oracle remediation on Windows OS.